FISMA is not just a paperwork exercise
FISMA sets the stage for establishing a strong security program, one centered around ensuring your baseline inventory, configuration management, patch management and vulnerability management regularly. Once the program is established, it is then validated by an independent assessment and authorized by the government authorizing official.
Agencies have different processes
Unlike FedRAMP, there is no standard process for FISMA compliance. Yes, the requirements are set forth in NIST SP 800-53, but each federal agency can tailor the baseline set of security controls and develop its own templates and process for testing. Fortreum recommends obtaining these process updates and templates upfront to further support a successful authorization journey.
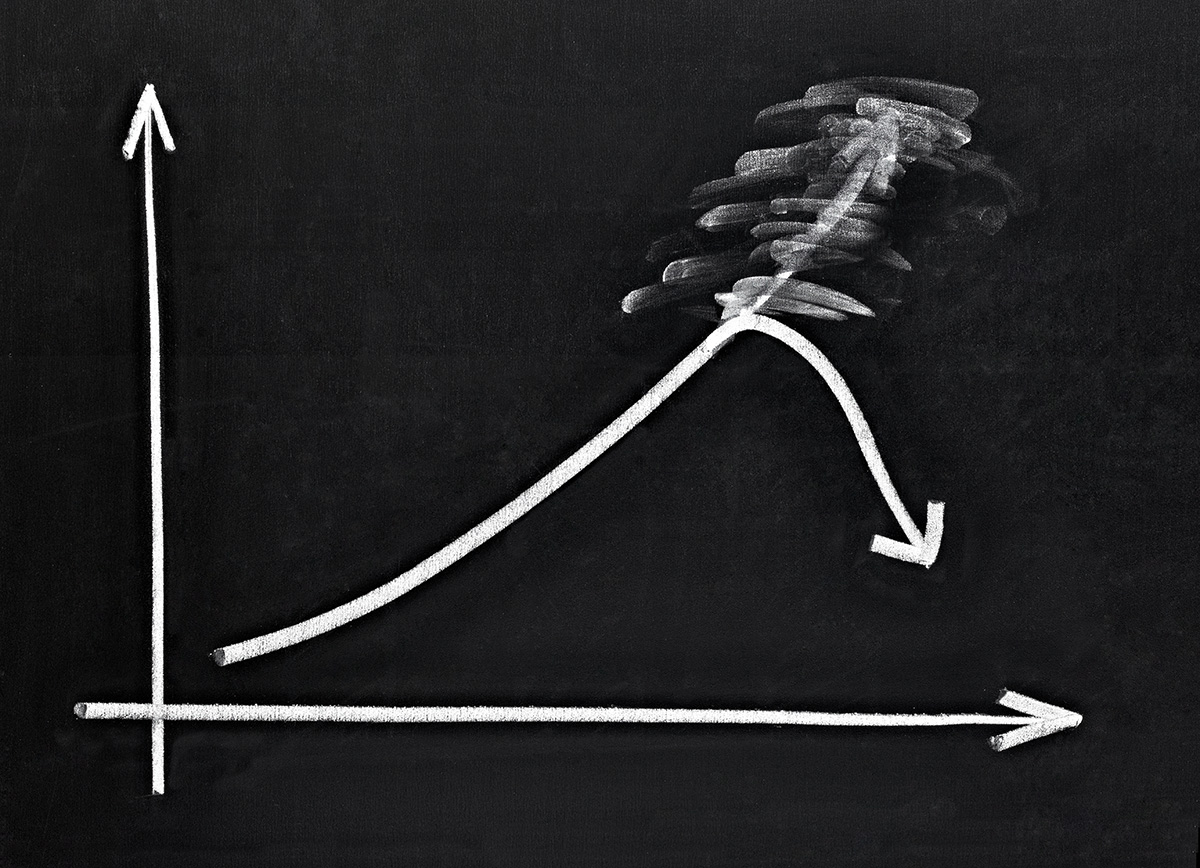
Vulnerability Management is Key
Through its many engagements, Fortreum has that the vast majority of findings are from missing patches or improper configurations. Many of these findings are uncovered during a credentialed vulnerability scans. Fortreum always recommends one be performed to provide both the vendor and government confidence that the IT service is protected from known vulnerabilities.
Assessment re-use is not common
Each federal agency is unique and each IT service that is leveraged must be assessed and carried under that agency’s FISMA authorization boundary. This means for every federal customer you do business with, your organization will undergo an assessment, even if it’s the same offering in a different federal agency.