Table of Content
DoD Cloud Authorization
The Federal Risk and Authorization Management Program (FedRAMP) authorization process can be a daunting endeavor – even for large-scale companies with mature and established security programs. Building on this FedRAMP baseline and extending cloud authorizations to the Department of Defense (DoD) Cloud Computing Security Requirements Guide (CC SRG) is even more complex. Most Cloud Service Providers (CSP’s) looking to sell to the US government typically start out with a crawl – walk – run maturity model. First a CSP’s Cloud Service Offering (CSO) must FedRAMP authorized, and at minimum, be classified under FIPS-199 as a FedRAMP Moderate baseline system. As if implementing 325 security controls for a FedRAMP Moderate system isn’t a feat in itself, the DoD requires more stringent security controls and process than those imposed on other government agencies, along with a separate authorization evaluation and authorization process managed by the Defense Information Systems Agency (DISA). Although there is some reciprocity for FedRAMP Moderate systems for IL-2 and FedRAMP High for IL-4, ensuring a system meets all the requirements as specified in DISA’s DoD CC SRG requires a CSP to a sound plan and company investment.
We often get questions around the overall DoD Cloud Authorization process, timeline, and technical challenges. This is too big of a topic area to cover – let’s first start by addressing the overall DoD cloud authorization process and look to further describe key milestones/gates in future posts.
Why Does It Matter?
Enabling enterprise-wide cloud technologies for the DoD is critical for the country. This presents a big opportunity for CSP’s but there is significant runway involved in being ready for business.
DoD CIO published a memo in December 2014 regarding updated guidance on the use of Commercial Cloud Computing services for DoD component entities. The memo establishes a framework for DoD components to obtain cloud services in accordance with the security requirements outlined in the Federal FedRAMP and the DISA CC SRG.
Similar to FedRAMP, if a CSP wants to sell a cloud service offering to DoD entity, the specific offering must obtain a DoD Provisional Authorization (PA). This is above and beyond what is covered in FedRAMP and is defined within the DoD Security Requirements Guide (SRG). If there is no DoD PA in place, then the cloud service offering cannot be utilized by any DoD organization.
The short of it – if your selling cloud services to the Department of Defense – you must adhere to the following guidance published by FedRAMP + DoD Cloud Computing Security Requirements Guide v1r3 DoD SRG for all offerings handling data classified up to SECRET. Cloud offerings at SECRET (IL6) must follow existing applicable DoD and Intelligence Community (IC) policies and are not covered by this CC SRG.
DISA Cloud Assessment Division
The DISA Cloud Assessment Division is an organization CSPs will inevitably be familiar with as they navigate through the DoD PA process. They provide support to DoD Component Sponsors/Mission Owners for all DOD cloud authorization lifecycles (pre-screening, assessment, validation, authorization, and continuous monitoring). It’s also important to note – they serve as reviewers on the FedRAMP Joint Authorization Board (JAB) for JAB cloud provisional authorizations.
“All DoD Cloud authorizations must be proxied through the DoD DISA Cloud Assessment Division”
If you want to sell cloud services to the DoD, you will need to become familiar with FedRAMP and the DISA cloud authorization process as they are the gatekeeper for DoD cloud.
DoD Cloud Authorization Terminology
It’s important to understand DoD cloud authorization terminology and paths to best position your organization through the DoD authorization process. DoD has provided the following paths to consider:
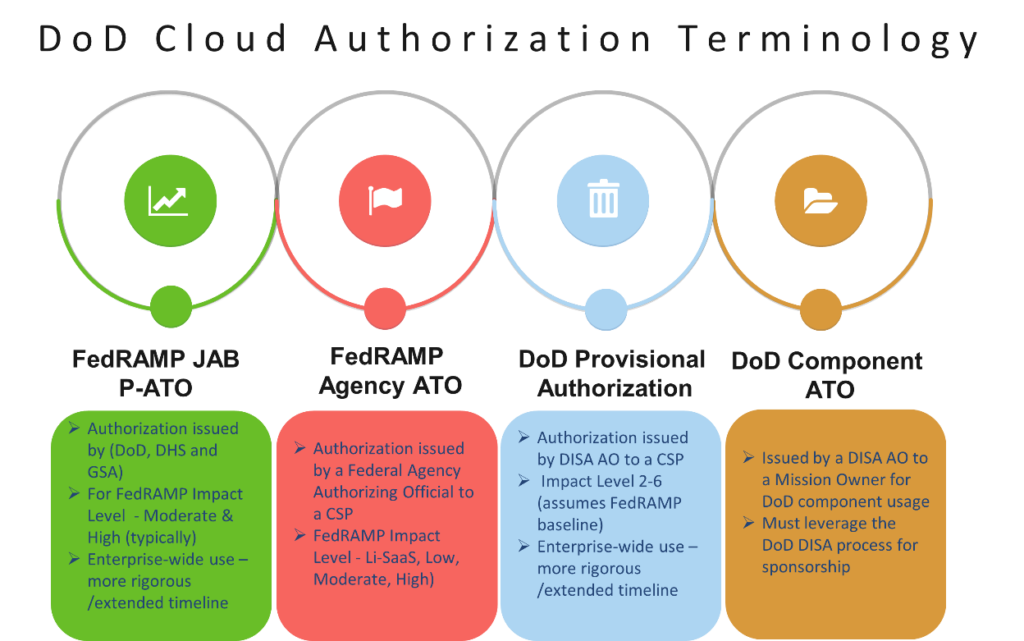
DoD cloud authorization paths that cloud service providers should evaluate and focus on are:
- Provisional Authorizations – Focuses on Cloud Service Offering Risks
- Issued by the FedRAMP JAB and the DISA Authorizing Official (AO)
- Component ATO’s – Focused on Mission Risk
- Issued by DoD Component/s Authorizing Official
DISA Cloud Assessment Division
The DISA Cloud Assessment Division (someone you/CSP should become very familiar with) provides support to DoD Component Sponsors/Mission Owners for all DOD cloud authorization lifecycles (pre-screening, assessment, validation, authorization and continuous monitoring). It’s also important to note – they serve as reviewers on the FedRAMP Joint Authorization Board (JAB) for JAB cloud provisional authorizations.
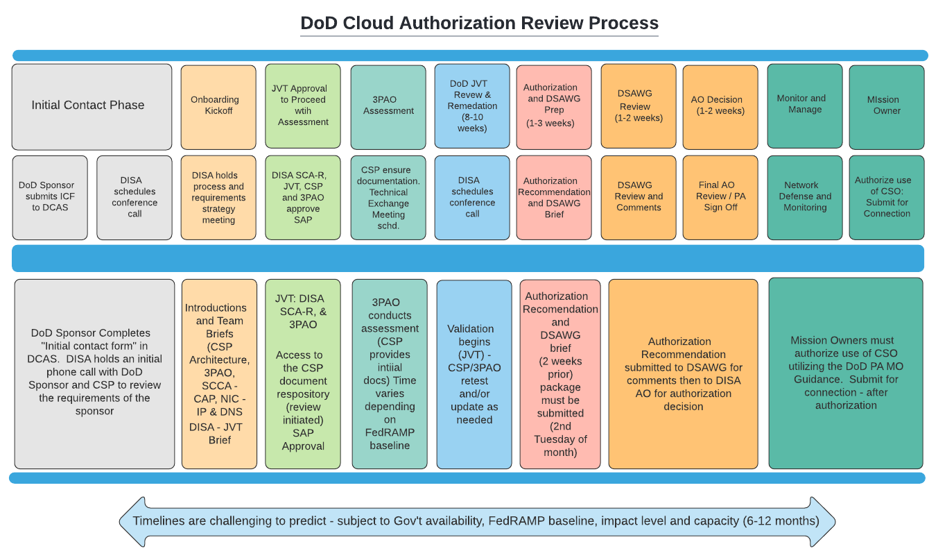
Roadmap to a DoD Provision Authorization (PA)
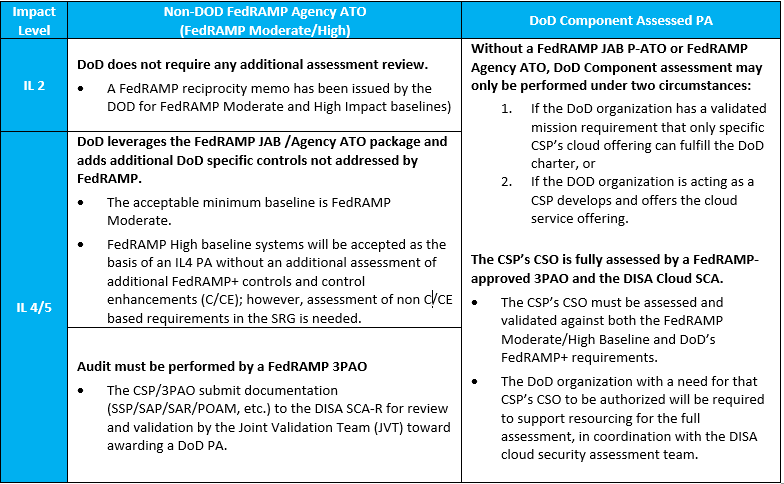
Note, that DoD preferred path to a DoD PA is the JAB P-ATO route, since the DoD CIO and DISA (JAB DoD Reviewers) are involved in the authorization process. Additionally, it’s in the best interest of a CSP to be assessed for both FedRAMP and DoD requirements simultaneously by the same 3PAO. Doing so reduces redundancies in assessments when having a CSO included in both the FedRAMP and DoD Cloud Catalog. For all DoD cloud offerings – the DISA Authorizing Official (AO) is the AO for all DoD PA’s. The PA is issued with conditions and usage considerations for the DoD Mission Owner. As with all FedRAMP / DOD accreditations, CSP’s must continue to comply with the ongoing Continuous Monitoring requirements to maintain their respective authorizations.
DoD Information Impact Levels (Levels 2 – 6)
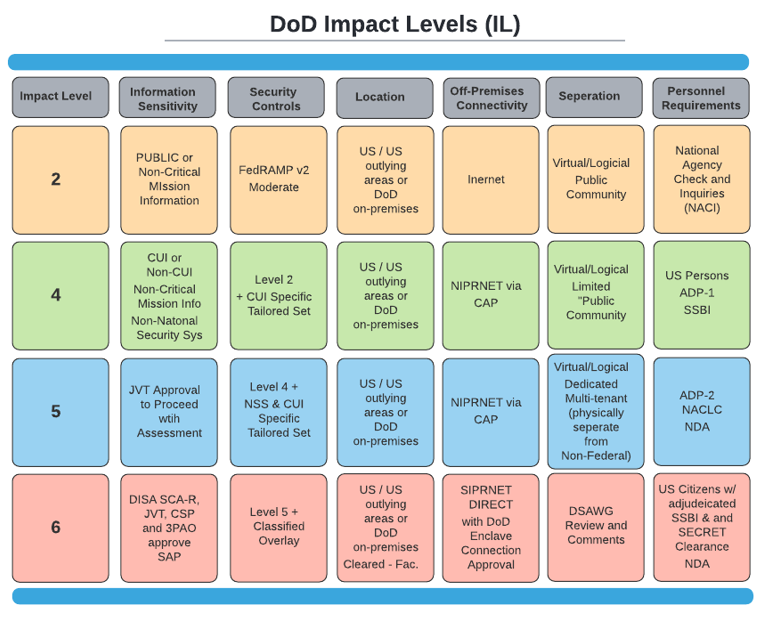
Most cloud organizations hire US Public Sector (DoD focused) seasoned sales teams to start generating the total addressable market for DoD cloud opportunities. The business case can be lucrative for the higher impact levels, but additional work must be done. As mentioned earlier, if you achieve a FedRAMP Moderate authorization – that is the equivalent of a DoD SRG Impact Level 2. However, if you want to continue scaling your cloud offering to higher impact levels, the security controls and organizational support model will need to adapt more to be successful. Look at DoD impact levels as security gates – you can’t see what’s behind the next iron gate unless you are cleared (approved) to do so. DoD SRG impacts levels define just that – they define additional security criteria, architecture and organizational provisions to be in place before you get a key to that gate.
“Cloud security information impact levels are defined by the combination the sensitivity or confidentiality level of information (e.g., public, private, classified, etc.) to be stored and processed in the CSP environment; and the potential impact of an event that results in the loss of confidentiality, integrity, or availability of that information.” * (DoD SRG v1.3)
Look at your potential business pipelines and opportunities – most (if not all) will have the DoD SRG impact levels (in addition to other things) defined in the business opportunity. It is up to the DoD to define the impact levels – its up to the contract/CSP to adhere to them. The table below defines the current DoD Impact Levels with high level terms.
Cloud Authorization Review Process/Timeline
Business authorization timelines can be a heated topic when business opportunity and commitments are on the line. The outlined schedule below is what DoD provides organizations need to plan on extra time to account for capacity challenges and review periods going longer. Just remember, there are things you can control and things you cannot – do not forget that! Make sure you’re setting the right expectations internally on how long things can take and what you can manage from a timeline perspective.
Summary
Providing cloud services to the DoD represents a significant business opportunity for organizations. Your leadership team needs to have the right business understanding of people, process, technology and timeline to make the investment required to meet the stringent requirements of the DoD. Successful DoD cloud authorizations can have significant impact specific contract awards but also sets a high security bar for selling into other industries. (If replicated across all organizational offerings).




