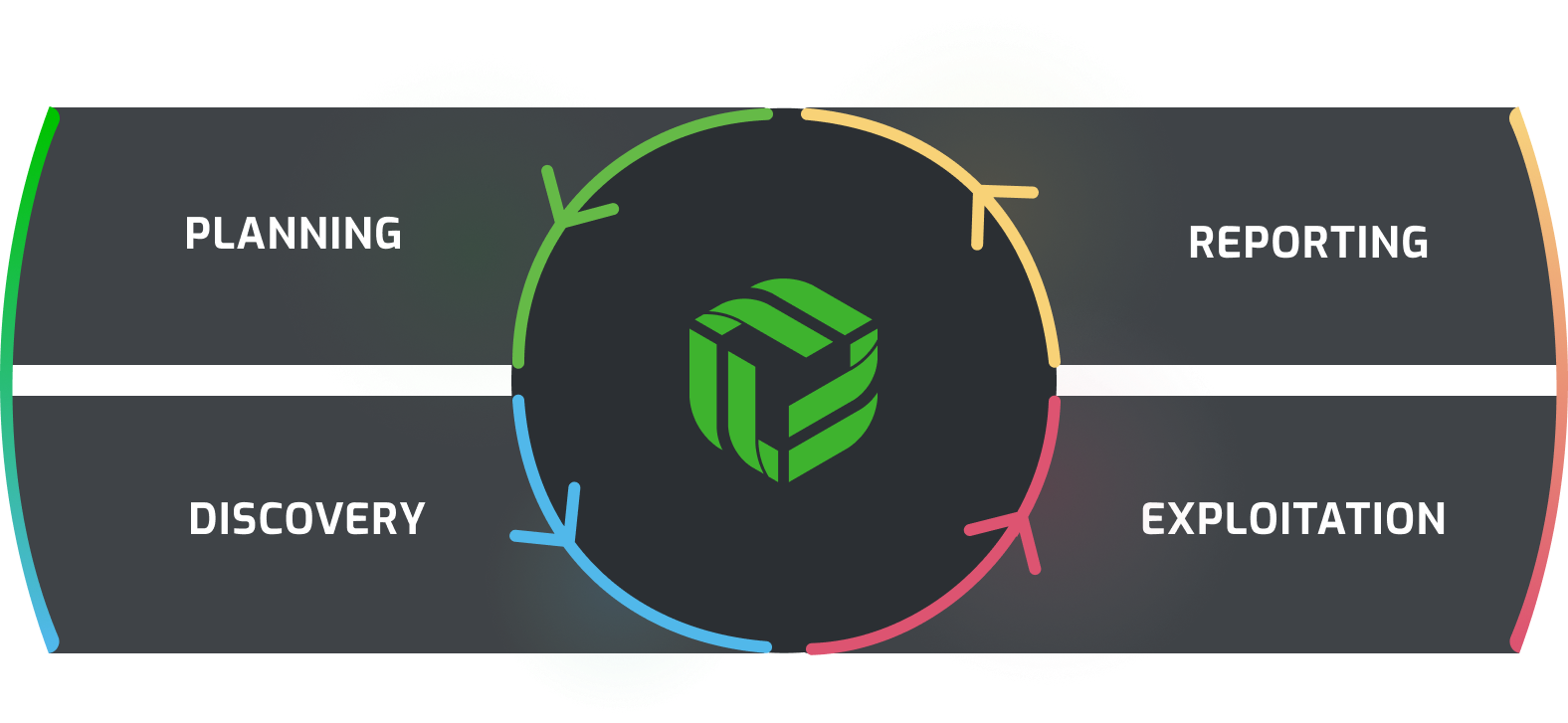
Get expert-level assessments with our enterprise, red team, and purple team evaluations that mimic real-world cyber-attacks. Red teams act as external attackers, while purple teams blend offense (red) and defense (blue) for collaborative insights into your organization. These activities can include:
- Enterprise Assessments
- Red Team Assessments
- Purple Team Assessments
Advanced evaluations use external and internal penetration tests to mimic real-world attacks, assessing your organization’s security. We spot vulnerabilities from both inside and outside your network, offering actionable steps for improvement. Our compliance testing ensures you meet industry standards, fortifying your security foundation. These activities can include:
- Network Penetration Test
- Application Penetration Test
- Compliance Based Penetration Testing
Starting with our foundational level evaluations, we first assess vulnerabilities within your organizational footprint. Internal assessments identify risks inside the organization, while external evaluations assess threats from an outsider’s perspective. Our goal is to assist you in pinpointing and tackling security weaknesses effectively to establish a foundational security posture. These activities can include:
- External Attack Surface Analysis
- Vulnerability Assessments
- Social Engineering